Cyber security is a major concern for small businesses, individuals, large enterprises, the government and essentially anyone who participates in modern society. It is such a concern that, in February 2016, President Obama created the Cybersecurity National Action Plan (CNAP), and appointed the first ever chief information security officer of the federal government. As cyber criminals ratchet up in sophistication and attacks become more brazen, the need for a deeper focus on cyber security risk management is becoming startlingly apparent.
How does your organization deal with cyber security risk management? The following are fundamental best practices that can help guide you as you review or implement your organization’s cyber security risk management program.
Focus on Internal Threats
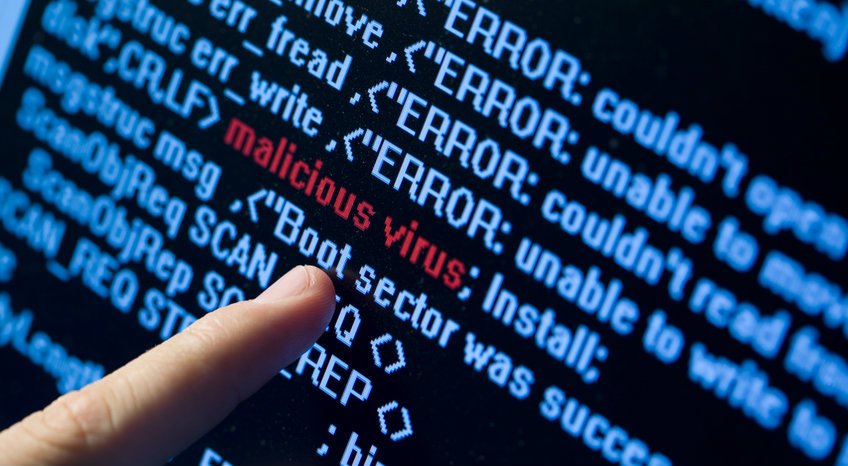
According to Security Week, “Despite increased investments in perimeter defenses” internal threats from employees and third parties including contractors and vendors account for 60% of security incidents. Human error or those with malicious intent are the internal threats that account for that 60%.”
Similarly, Computer Weekly wrote,
“Overall, 70% of all incidents reported by government bodies were due to disclosure of data in error, which suggests reducing or identifying possible signs of human error or anomalous activity should be a priority.”
Implementing a solid employee training policy on cyber security that is clear and widely communicated is important.
Yet, it is critical that employees are aware of how their actions could severely affect the company and what they can do to ensure they aren’t putting the business or themselves at risk. Bringing continual awareness as opposed to a one-time training is important. In fact, continual awareness is so important that President Obama plans to run a cyber security awareness campaign as part of CNAP.
Another critical tactic in combating internal threats is to closely manage and monitor third parties such as vendors and contractors. Currently, most businesses have very lax security and onboarding protocols for third parties and as a result, third parties have been responsible for a large number of enterprise level security breaches. Companies like SecZetta are on the forefront of helping businesses better manage third parties through identity and access management.
Continuous Monitoring and Record-Keeping
Continuous monitoring and record-keeping are crucial aspects of a reliable cyber security risk management program and can help organizations act protectively rather than reactively when it comes to security. As TripWire said,
“On the drawing board, continuous monitoring is an approach that can catalyze truly immediate detection and response in the event of an attack on any system. It may appear to be a quantum leap forward in the quest to adopt a proactive, rather than reactive, security model. Plus, many of today’s existing security tools can be leveraged in continuous monitoring.”
And Power Magazine explained the importance record-keeping, noting,
“Without good logs, it may be impossible to determine whether or not there was an actual intrusion, or, if that is known, how far it went and what damage was done. Knowing what happened makes a company much better prepared for dealing with regulators and for responding to potential litigation. Being able to establish that an intrusion was unsuccessful or that damage was limited puts a generator in a much better position than if the scope of events remains unclear.”
Continuous monitoring and record-keeping should be a foundational element of a strong cyber security risk management program.
Cyber Risk Visualization

Visualization can help both security experts as well as business owners and those without deep training in IT security, by mapping out networks and identifying patterns. As Tripwire wrote,
“Using dynamic and interactive visualization to tract these patterns, you can vastly reduce the time it takes to find and understand network breaches, and give analysts more insights into the workings of malware. These patterns can also help companies identify malicious software or behaviour that may not have been found without the ability to track them as they move laterally within a system.”
Cyber visualization takes complex information and simplifies it, making it easier to detect breaches and mitigate threats — something every business can benefit from.
Cyber Security Insurance
If you work in security, you know that no system or strategy is fool proof. That’s why cyber security insurance can be so beneficial to enterprises in helping to round out a strong cyber security risk management program. Currently, the cyber security insurance market is growing, with close to 100 providers offering insurance products. Yet, adoption is slow with only around 2% of companies owning cyber security insurance according to Julian Waits, President & CEO at PivotPoint Risk Analytics. However, with the industry in its infancy, the experts only expect this market to grow as more and more businesses realize the critical need for cyber security insurance.
In addition to these three practices, closed-loop remediation and risk-based prioritization should be looked at as additional best practices when implementing a cyber security risk management program.
At the University of San Diego we are helping to lead the way in cyber security mitigation through training professionals in both cyber security engineering and cyber security operations and leadership. If you would like to take your education to the next level and become a leader in the field, consider a master’s degree in cyber security operations and leadership from USD. Contact an admissions representative to learn more about our online and on campus programs.