Master of Science in Cyber Security Operations and Leadership
Program Outcomes

Interested in the Program?
Get in touch with an advisor today and ask for your Application Fee Waiver Code
"*" indicates required fields
Program Outcomes
What can I do with a cybersecurity degree? Will a master’s degree really give me a technical advantage? Is this a lucrative career path? These are all common questions we get in regard to cybersecurity. The future is bright and the opportunities are abundant. If after reviewing this page you have any further questions about the cybersecurity landscape, please don’t hesitate to contact our team at (619) 260-4580 or use the chat feature on this page.

Industry Insights
The cybersecurity talent shortage is undeniable. Amid the ongoing explosion of data breaches and cybercrime, demand for cybersecurity professionals with the right experience and education far outpaces the supply.
Another factor complicating the cybersecurity staffing situation: The intense demand and competition for talent is causing high turnover in cybersecurity jobs. This means companies are having trouble retaining their existing talent AND skilled workers are getting contacted by recruiters, even when they are not actively looking.
For the companies and organizations that are struggling to stay ahead of the hackers, this higher-than-average job turnover represents an “existential threat,” according to Infosecurity Magazine.
But for workers, the report suggests, “cybersecurity skills are a sellers’ market, where experienced professionals can easily find lucrative offers to leave one employer for another.”
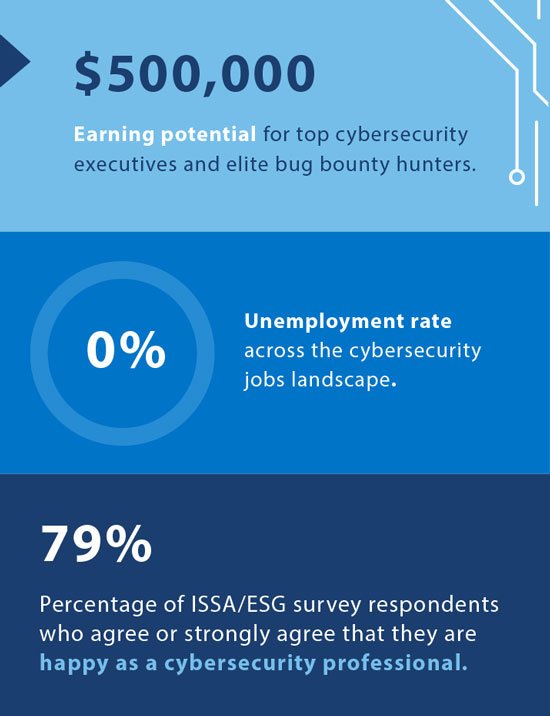
According to a comprehensive study conducted by the Information Systems Security Association and the Enterprise Strategy Group, an independent industry analyst firm: “Any employer that has tried to recruit cybersecurity talent in the recent past knows how big a challenge it is. The competition is fierce.” The research reveals that:
- 46% of cybersecurity professionals are contacted weekly by recruiters, regardless of whether they are actively looking for a job.
- 18% of cybersecurity professionals not seeking a new job receive contact daily from recruiters.
- Fortunately, 79% of survey respondents agree or strongly agree that they are happy as a cybersecurity professional.
PROGRAM OUTCOMES
1: Develops specialized field knowledge and integrates knowledge across content areas of Cyber Security.
2: Demonstrate critical inquiry through field-based approaches and methods and through effective and ethical information search strategies.
3: Applies learning across multiple contexts within the field, integrating knowledge and practice specifically relating to the areas of cybersecurity and leadership.
4: Reasons ethically in evaluating general perspectives, policies, and/or practices relevant to cyber security as well as evaluating diverse points of view to include temporal, cultural, linguistic, sociopolitical and/or technological contexts.
Career Outlooks
The talent shortage has created a “seller’s market” for skilled cybersecurity professionals, with countless organizations across all industries paying six-figure salaries for top talent.
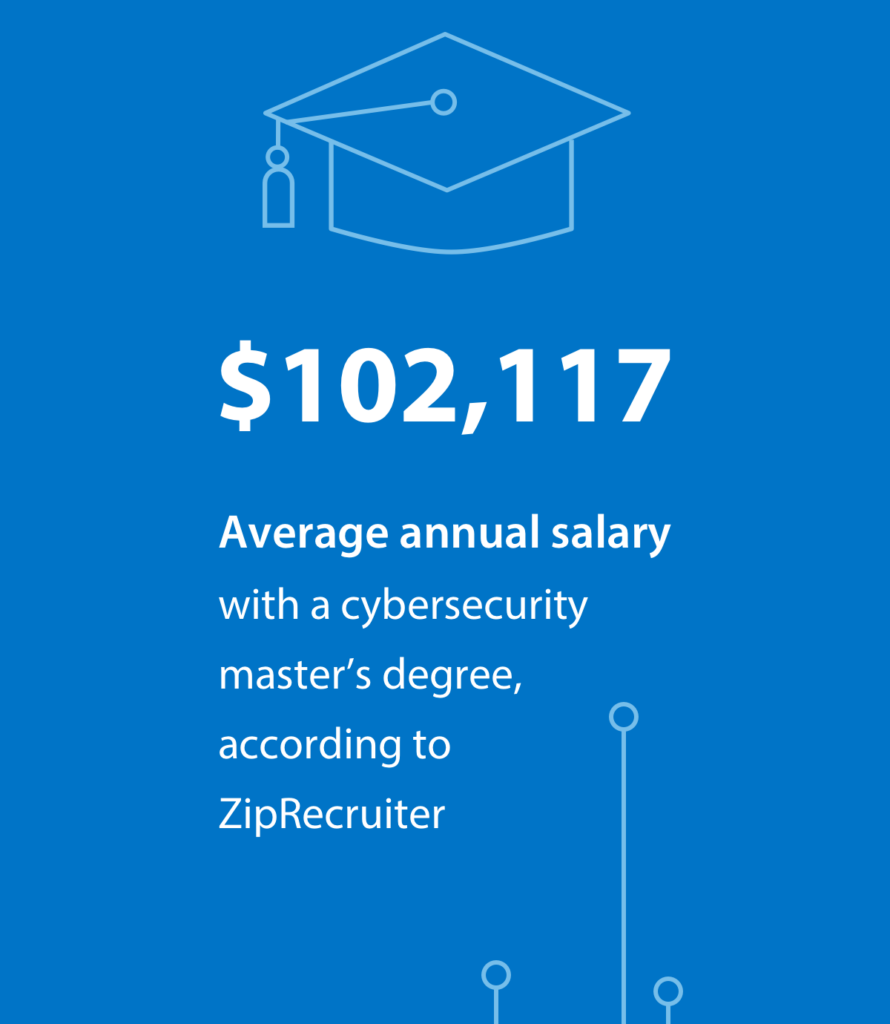
Educational Advantages
There is no doubt about it, a master’s degree can give a valuable technical advantage in the workforce. According to ZipRecruiter, the average annual salary with a cybersecurity master’s degree is $102,117. (Note: The cited salary represents the value of the current market; actual salary amounts are dynamic and may change daily.)
“Part of our role in helping to train current and future generations of cybersecurity professionals is to conduct research and collaborate with key industry stakeholders to ensure that our curriculum is cutting edge and that our training aligns with the workplace needs of employers.”
– Dr. Michelle Moore
Academic Director, University of San Diego’s Master of Science in Cyber Security Operations
What Can You Do with a Cyber Degree?
A quick search for cybersecurity jobs at leading employment websites LinkedIn, Indeed.com and Monster.com reveals a wealth of openings across the country spanning all experience and seniority levels.
Examples of cybersecurity careers include:
| Cybersecurity Infrastructure Manager | This position helps secure important infrastructure (highways, bridges, tunnels, etc.) from terrorist attacks and works with others to increase security in public places and other “soft targets.” |
| Lead Cybersecurity Engineer | This senior-level engineering position demonstrates top coding and leadership skills. |
| Cybersecurity Analyst | As a cybersecurity analyst, you will plan and implement security measures to protect the computer networks and systems of a company or organization. |
| Cybersecurity Manager | Also known as information security managers and information systems security managers, these professionals identify potential areas of vulnerability. They also enhance security to safeguard valuable company data and typically manage the information systems team. |
| Chief Information Security Officer (CISO) | This is the executively chiefly responsible for an organization’s information and data security. |
| Cloud Cybersecurity Analyst | This role helps design and construct cloud security architectures and reviews and analyzes cloud security measures. |
| Cybersecurity Forensics Professional | A digital forensics professional works on a cyber crime — in other words, information that has been stolen (or illegally passed through) electronic and digital devices such as cell phones, computers, networks, etc. |
| Cybersecurity Consultant | A cybersecurity consultant is a professional who assesses the security and risk of a business or organization and provides solutions and recommendations on safety measures, protection and best practices. This position could work directly for an organization or provide consulting services. |
| Vice President, Information and Cybersecurity | This position is similar to the high-level CISO role in which a person helps maintain and improve an organization’s information and data security measures. |
| Product Marketing Manager – Cybersecurity | This position focuses on the brand messaging and marketing of cybersecurity products and services. |
| Cybersecurity SME with Security Clearance | A cybersecurity subject matter expert (SME) could specialize in a variety of topics, such as Intelligence, Surveillance and Reconnaissance (ISR) or federal information security. Clearances are typically required for cyber jobs in government agencies (FBI, NSA, CIA, etc.), government contractors (Booz Allen Hamilton, Leidos, Lockheed Martin, etc.) and organizations that work with government contractors. There are three types of security clearances: confidential, secret and top secret. |
| Cybersecurity News Writer | This news writer works for a media outlet (newspaper, television station, etc.), a general interest or niche magazine, or a particular company/website that focuses on cybersecurity issues. Writing may include articles, blog posts, press releases, social media content and newsletters. |
| Cybersecurity Developer | This type of developer creates computer programs that help keep systems, networks and information safe. |
| Lead Cybersecurity Threat Hunter | As the name implies, this position seeks out and monitors cyber threats and typically works within a team to improve threat detection and improve overall security measures. |
| Program Manager – Cybersecurity | This position typically heads up a cybersecurity program and may also be called compliance manager, program lead, IT governance manager, portfolio manager or IT infrastructure/security manager. |
| Cybersecurity Specialist | Often called information (IT) security specialists or network security specialists, people in these positions play a central role in securing the information systems of businesses and other organizations. |
| Cybersecurity Incident Response Manage | A person in this role helps to identify, analyze and figure out how a business or organization will respond to a security incident. |
| Network Administrator | Network administrators are responsible for the daily operations of computer networks. They typically design, manage and maintain networks, helping to oversee LANs, WANs, network segments and other systems. |
| Systems Administrator | A systems administrator is responsible for the maintenance and operation of the computer systems and servers. This includes software installation and updates, participating in research and development and resolving issues related to computers and server systems. |
| Ethical Hacker | Ethical hackers are paid to try to break into computer systems. They are involved in penetration testing, vulnerability assessments and a range of strategies intended to keep their organizations safe from cyber attacks. |
| Security Auditor | Security auditors work with companies and organizations to provide comprehensive audits of online security systems. |
| Cybersecurity Consultant | A person in this position assesses the security and risk of a business or organization and ultimately provides solutions and recommendations on safety measures and protection. |
| Cybersecurity Architect | A cybersecurity architect is a senior-level position responsible for planning, designing, testing, implementing and maintaining an organization’s computer and network security infrastructure. |
| Penetration Tester | The professionals performing this job are a specific type of ethical hacker. Many large organizations are hiring full-time employees or third-party contractors to infiltrate their computer systems to detect and address vulnerabilities that could be exploited by cyber criminals. |
| Information Security Analyst | Named the #1 in 100 Best Jobs by U.S. News & World Report, professionals in these positions are described as “the gatekeepers or security guards of information systems” due to their scope of responsibilities related to preventing, monitoring and responding to data breaches and cyber attacks. |

The Latest
Cybersecurity News
Stay ahead of the curve with the latest news, trends, and industry insights — plus updates on what’s happening with USD’s cybersecurity programs. Subscribe today!
Where Do Your Graduates Work?
Getting a graduate degree is a leg up in the cybersecurity industry and our alumni are actively working to protect systems around the world. Here are just some of the companies that our graduates work for:
USD Cybersecurity Alumni
Discover how an advanced degree in cybersecurity from the University of San Diego helped these skilled professionals take their career to the next level.
Adrian Villegas is proof that you don’t need a technical background to transition to cybersecurity. Learn how USD’s master’s degree program was the perfect fit for Adrian’s schedule and his desire to transition to a more challenging career.
If you are fascinated by the idea of a career in cybersecurity but daunted by the challenge of earning your master’s degree, you’ll want to read Kylee’s story. Learn how an advanced degree from USD played a key role in Kylee’s journey from American Idol to a tech company dream job.
Getting hacked can be a devastating experience. But for Lynn Hijar Hoffman, having her work website hijacked somehow felt more like an opportunity. It also set her on a course to earn her master’s degree in cybersecurity at the University of San Diego and, ultimately, to start her own company.
What if you could graduate from a cybersecurity master’s degree program and walk straight into a dream job at one of the world’s top tech companies? With such high demand for trained cybersecurity professionals, this scenario is more realistic than ever. Just ask Paul Cho, who earned his cybersecurity master’s degree in May 2019 and started work as a security engineer at Salesforce in May 2019.
Chart Your Path in Cybersecurity
Discover which USD online cybersecurity master’s program aligns with your career goals.